Audio captured by your webcam mic could be used to spy on your screen
Researchers have discovered a way to spy on content displayed on computer screens remotely, simply by processing the audio picked-up by the webcam microphone.
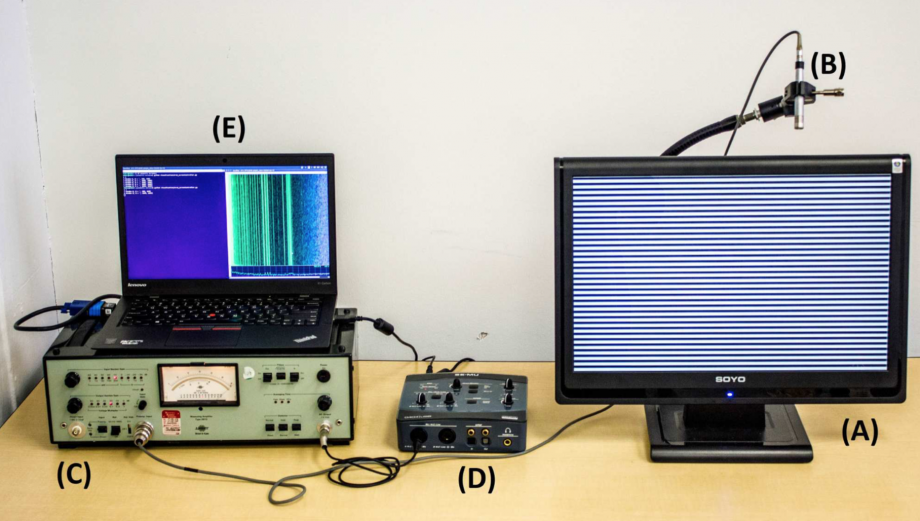
The CRYPTO 2018 conference saw the publication of worrying research outlining how a side-channel attack dubbed Synesthesia could utilise “content-dependent acoustic leakage from LCD screens” to reveal on-screen imagery.
Effectively, this acoustic leakage from the displays could allow attackers to build up a visual picture and, as well as the microphones in built-in webcams, nearby smart speakers and mics in mobile devices are capable of picking up this LCD leakage.
For example, audio from a video call could be analysed and processed through machine learning tools to determine what the parties were looking at on the screen at any given moment. During its testing, using the audio captured from a Google Hangouts call, the researchers were able to identify which of ten websites were on screen at the time with 96.5% accuracy.
Read more: Internet Security: A power user’s guide
Within the study, researchers from the University of Michigan, Cornell, Penn, and the University of Tel Aviv explain how the leakage signal makes it simple to distinguish between repetitive images displayed on the target monitor.
It created a simple program that shows patterns based on those signals, which clearly changed when the content on the monitor changed. Using the machine learning techniques the team was then able to build up a picture of the content on screen.
In some cases the researchers were also able to identify large font text, while, in a different experiment, the researchers were also able to reliably capture keyboard strokes on a smartphone or tablet based upon the same acoustic leakage.
As VentureBeat points out in its report, it’s food for thought for those working with sensitive data.
Is this research something we should all be concerned about? Drop us a line @TrustedReviews on Twitter.


