KeyPass ransomware is infecting computers around the world

A new form of ransomware is spreading fast. KeyPass – a variant of the STOP ransomware – has managed to hit hundreds of computers in more than 20 countries since first emerging on August 8.
Researchers from Kaspersky Lab have taken a look at KeyPass (distinct from KeePass – a popular and safe password manager), and found a hidden additional option where attackers can take control of an infected system, which hints at more advanced attacks to come.
Read more: Best smartphone
Other than that, it’s a pretty familiar ransomware story. Once infected, the computer gets to work encrypting all of a user’s files in a key only known to the hackers.
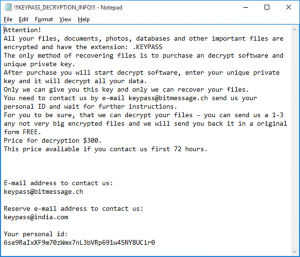
A ransom note is left on the computer’s desktop demanding the victim contact the cybercriminals for instructions of how to pay a $300 fee in order that their files are returned to them. The note hints that the price will increase if the victim doesn’t make contact within three days.
As KeyPass turns a legitimate part of computer security – encrypting files – against the user, there’s not a great deal that can be done once a user has been infected. The best means of defence is ensuring you don’t get infected with ransomware in the first place, and in this case, that means being vigilant about software downloads.
Plus, if you regularly backup your important files to a non-connected drive, you’ll be in a position to ignore these extortion attempts when they come in.
Security experts advise victims not to pay the ransomware criminals if they’re extorted. This is partly because it encourages crooks to keep at it, and partly because it can also mark you specifically as a target who is likely to pay up, increasing attacks aimed specifically at you.
Plus, of course, you’d be putting your faith in a criminal, and there’s no guarantee they will actually unlock your files even if you pay up the ransom in full.
Have you ever been infected with ransomware? How did it turn out? Let us know on Twitter @TrustedReviews.


