How to become anonymous online

We guide you through the process of remaining anonymous online, so you can browse in confidence.
Our communications have, since we started using digital means, been an easy target for nefarious hackers. But let’s face it, how many of us are actively taking measures to be anonymous online?
As long as we use some kind of traceable form of communication, then there will groups who will attempt to access and infiltrate that communication. Therefore we need to do something that will make their jobs a little more difficult.
We’re not saying that you can be totally anonymous, such a thing is virtually impossible (although doable, if you know how to manipulate IP addresses and so on). The resources the groups on the other side of the digital line have are, by our standards, limitless, but what we can do is attempt to make our online communications somewhat more clandestine.
Becoming anonymous, the basics
Before we go into the more selective processes of encryption and using any third party tools or utilities, we’ll start with some of the basics of keeping your privacy and avoiding spammers and scammers as much as possible.
Be Incognito
Private browsing mode, or Incognito mode is a feature that has rapidly become the second most used option in current web browsers. Despite its alternative name, ‘porn mode’, using the private browsing function beyond sites of scantily clad ladies is perfectly acceptable for instances where you could be on another users’ computer, and you want to check your Facebook, Twitter or online mail accounts.
Similarly it’s perfect for testing sites that are heavily laden with cookies, and it’s good for those times where you have access to a public computer, or even on your home PC, and you don’t want any sites knowing where you’ve previously been.
Private browsing isn’t totally fingerprint free, items such as DNS lookups and certain cookies can stay behind after a private browsing session, so it’s best to treat private browsing as a temporary, perhaps on-the-go mode of being locally anonymous. And by that we mean it won’t store any of your browsing history on a public computer.
If you want to see a good example of this, open up a private browsing session and browse through a number of sites, then exit the session, drop into a Command Prompt and type in the following:
ipconfig /displaydns, and press Enter.
This will list all the cached DNS entries that your computer, regardless of whether you used a private browsing session or not, has visited.
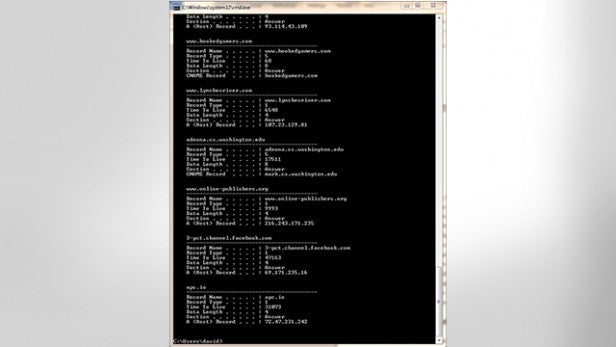
To remove the entries, enter the following:
ipconfig /flushdns, and press Enter.
This way, the list will be clear and attempts to gain access to that list will be thwarted. A good idea could be to setup a batch file of some description, one that would launch the browser in private browsing mode, then when closed will automatically flush the DNS entries. It’s not 100% anonymity, but it can be used to retain a certain level of privacy.
False identities
Using a false identity sounds a lot more intriguing than it actually is, but in many ways it’s actually quite effective.
Consider this: you use your normal email address for logging into Facebook, Twitter, eBay and many other sites including some online gaming. It may sound perfectly reasonable, however, the ‘hacker’, or whoever, now has the very easy task of only hacking a single account, or tracing you back to the source with apparent ease. Now, if you had a set of aliases, then the ‘hacker’ would need more time and effort in tracing the false identity back to its true owner.
That’s a very basic concept, but one that can be used to successfully mask your usual online activity behind a string of false identities. Indeed, there are some circumstances whereby users have reported using in excess of fifty plus names and email addresses, all false in order to avoid entering their real identities into websites.
Think of this tactic as staying below the radar. There are very few reasons as to why you should provide your real identity online, unless you want the site to know your real name and address. Most of the time sites will only collate and sell on, or use your details for advertising purposes – and by no means should you ever give out your real email address, home address or contact details on a publicaly accessible website.
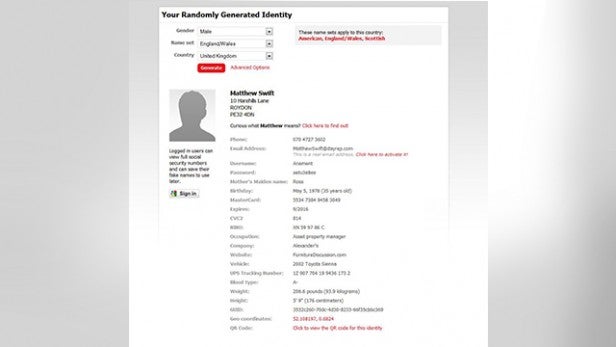
If you struggle coming up with fake identities, then consider using something like the Fake Name Generator, found here. This site can create an entire fake identity, including names, addresses, email and telephone numbers. It can even provide you with a fake credit card number, mother’s maiden name, vehicle, blood type, height, weight and a QR code in which to use. Obviously all the data supplied is fake, and any resemblance to a real person is purely coincidental.
In addition to the above Fake Name Generator, the false email it generates is actually capable of being activated and used as a free disposable email system with any incoming emails to it being displayed in the hyperlinked page. However, you don’t know who else has access to this system, so it’s best to treat it as an email that can be used on webforms or other sites that require you to spill the beans on who you really are.
3rd Party tools to stay invisible
Beyond the basics, there are a number of programs that can be installed to help cover your tracks, disguise your digital fingerprint or keep you invisible when online. The most well known of these is the Tor Network, which we’ll cover first, but for those who may require a more complete package of encryption and anonymity, then the likes of a VPN (Virtual Private Network) would be the order of the day.
The Tor Network
There has already been much said about the Tor Network, and how it can go a long way to making sure that your online activity is as anonymous as possible. But for those of you who don’t know, Tor is a method of bouncing your online communications through a distributed network of Tor relays, each of which is run by volunteers, from around the globe. In essence, its basic concept is to block sites from tracking you, from learning your physical location, and allows you to access otherwise blocked sites.
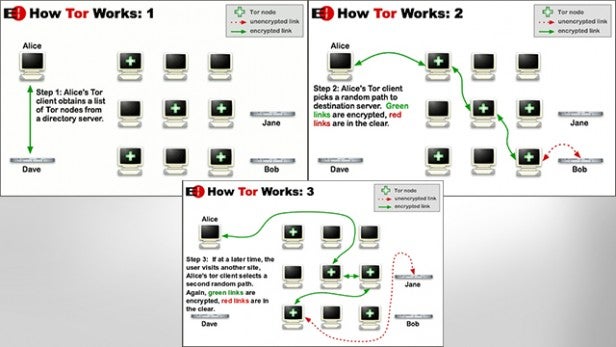
The Tor Browser Bundle is a free, portable, self-extracting package for Windows, Mac, and Linux that when run will automatically connect you to the Tor Network, and launch a specially designed and modified version of Firefox.
When it’s up and running, and when you start browsing via the Tor launched version of Firefox, all your connected online content is encrypted and routed through the aforementioned relays. The Tor Browser Bundle works effectively with any TCP applications, such as instant messengers, remote logins, and other web browsers. However, it’s not a 100% anonymity product, and it shouldn’t be used in order to download illegal music or films as this will put undue strain on the Tor network, and ruin it for legitimate users.
The protocols that are used in P2P sites are often used to scan your IP address as soon as it reaches you so it can send back the actual IP address rather than the Tor created one.
That said though, Tor is an excellent third party product to use if you want to stay anonymous for casual searching. The included Firefox version, based on Mozilla’s Extended Support Release (ESR) Firefox branch is patched to enhance the security and privacy functions. That includes blocking access to the Components.interfaces element which can be used to identify the users’ platform, blocking all plugins except for some Flash circumstances, stopping SSL sessions from caching their connections and stopping WebSockets from leaking DNS information.
Needless to say, by using the Tor Browser Bundle, with the Firefox instance that’s included with it, you’ll be relatively safe from online snooping from all but the most hardened of individuals.
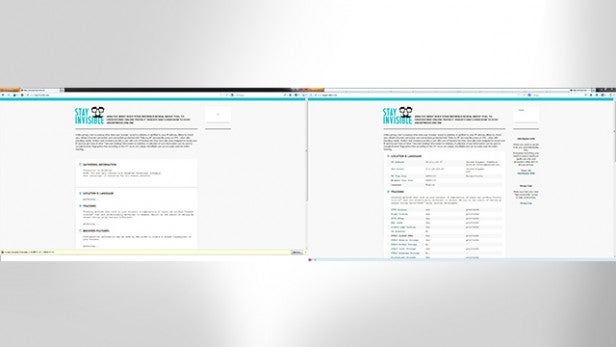
If you look at the example screen shot, using the site stayinvisible.com as an example, you can see that by navigating via the Tor version of Firefox, your IP address is hidden through Javascipt being disabled, and the patched version has successfully blocked the relative scripts needed to gain knowledge of your system.
If you want to try out the Tor Browser Bundle, and see just how successful at hiding your digital fingerprint is actually is, then point your browser towards the Tor website for access to the downloads section and further information on how Tor can help you stay relatively anonymous and safe when online.
HMA VPN
Despite its unusual name, Hide My Ass, and the fact that this is a paid for service (although there are free options available), HMA is actually a very impressive VPN service from the UK that will allow the user to hide their IP addresses, unblock certain websites, unlock region-restricted channels and surf anonymously through one of the company’s 50,000+ private and anonymous IP addresses.

HMA’s 934 VPN servers are located throughout 190+ countries and utilise the OpenVPN, PPTP and L2TP protocols. It’s an extremely useful and easy piece of software to use. Basically all you need to do is sign up for the service, either via the three available monthly payment plans: one month at £7.99, six months at £5.99, or one year at £4.99. Then it’s just a case of installing the software, entering your user name and password, and connecting.
All the hard work and configuring of the VPN is done automatically, along with a special built-in ‘Speed Guide’ feature which will auto select the fastest VPN for you based on your current location and connection.
The software is available for Windows, Mac, and Linux. It’s available for download via the HMA Control Panel, once you sign up for a package and an account, along with a selection of help files and tutorials.
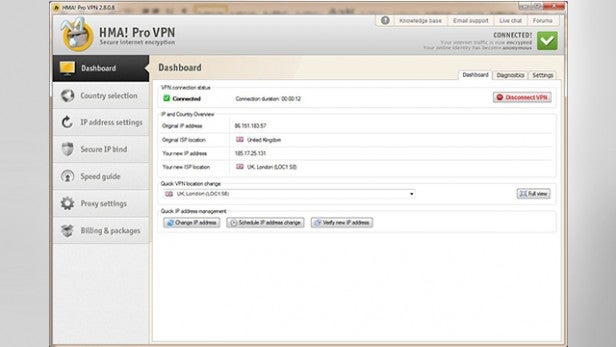
The packaged VPN manager software includes some rather nice features, alongside the speed guide. There are options to choose which VPN protocol you want to use, with OpenVPN being the more popular and possibly the faster of the protocol types, as well as options to randomly change IP address every few minutes as defined by the user.
There’s also a handy ‘Secure IP Bind’ feature, which will stop an application from going online without the HMA VPN connection running. You’re also able to manually select a particular country’s VPN server and configure the load balancing so you’ll be connected to the VPN server with the fewest number of users, and consequently more resources available for you.
CyberGhost
CyberGhost is a VPN that is widely regarded as one of the best forms of online protection a user can possibly ask for, and it just got a little bit better.
CyberGhost 5.5 has recently been released, and with it comes a number of additional benefits that can be added to your subscription package. Where simply hiding your IP address and encrypting your connection are the norm for a VPN, the team at CyberGhost feel that there’s more that needs to be done.

The new features added to the client interface include an Ad-Blocker, Malware and Virus Protection, Data Compression, Prevention of online tracking, the ability to force HTTPS, and access to even faster servers.
Advertising usually contains elements of location tracking, and viewing where a user has been previously. Malware and virus protection is an absolute must these days, and where most users will already have some form of protection installed on their computers, having that protective layer at the online server side is a fantastic addition.
The Data Compression feature greatly improves mobile browsing speeds and data tariffs, and the prevention of online tracking will actively remove any content that could be seen as monitoring your browser usage.
Finally, forcing HTTPS is a useful feature that many VPNs omit. By forcing a secure connection you’re increasing the security of your browsing, and lessening the chances of your online banking, for example, being hijacked by some hacking method.
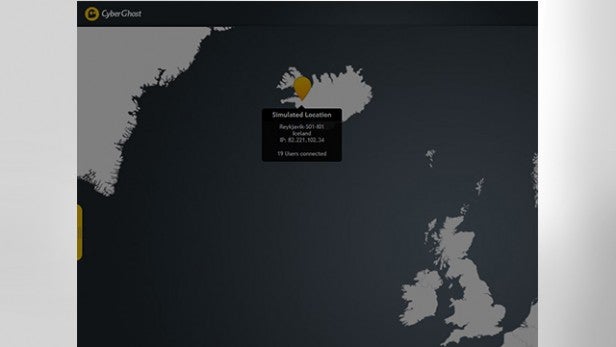
Beyond the new options, version 5.5 has a faster, slicker interface. Connection to the servers beyond the UK is quicker, and the overall download speeds are dramatically improved. There’s also a handy graph included, to show you how many instances of blocking, tracking and forcing of HTTPS have occurred during your use of CyberGhost.
If you’re serious about your privacy, and you want to surf anonymously without being logged or watched, then CyberGhost has a subscription package for you.
For more information, including pricing for the various subscription packages, visit the Cyber Ghost website.
Browser Add-ons
If you’re not too concerned about traffic other than what goes through your web browser being traced, then rather than installing a VPN consider using one of the many free browser add-ons that are available for IE, Chrome, and Firefox.
These can help stop individual scripts from running, pop-ups from appearing and tracking elements from finding out where you are.
DoNotTrackMe/Blur
DoNotTrackMe, or Blur as it’s now known, is the newly branded and improved version of DoNotTrackPlus, and has something in the region of 300 more advertising sites, and over 650 tracking technologies added to its black list from the previous versions.

It’s available for Chrome, IE, Safari and Firefox and can either be installed via the browsers add-on store or from the developer’s, Abine, site for free. Once it’s installed, and the browser is restarted, the DNTMe icon will appear and will start logging the attempts made by others to track your activity.
DNTMe is a good add-on to have installed on your browser. It doesn’t slow anything down, you can still view the same content as before, less some of the adverts that appear with a tracking element attached, and gives you medals for the number of tracking attempts it has blocked so far.
Adblock Plus
Adblock Plus is another free add-on for IE, Chrome, and Firefox and is regarded as one of the best add-ons for blocking phishing, tracking, and protecting you against malware and unwanted adverts.
Since its first appearance back in 2002, the Adblock extension has been consistently improved. It’s very easy to install, either from the browser’s add-on store or via adblockplus.org, and will protect your privacy to a relatively good extent by using a collection of filters. These filters can be added to, or custom filters can be used. However, be careful when using unknown filter lists, as they may let something through.
NoScript
NoScript is an add on, or extension, for Firefox, Seamonkey, and other Mozilla based web browsers. It’s free, open source, and blocks all JavaScript, Java, Flash, and other nefarious plugins unless otherwise trusted by you. It can be installed either via the Firefox add-on store, or from the NoScript site directly.

NoScript does an excellent job of masking your location, activity, and platform details from scripts that request that kind of information. This alone hides your digital fingerprint from the vast majority of sites available on the internet, and grants you a decent level of anonymity and privacy.
Final thoughts
As we said at the beginning, it’s almost impossible to become 100% anonymous while online. To do so would require some very secure VPN’s, a wealth of browser-based blocking techniques, and you’d probably have to be using a heavily customised operating system.
However, by using one, or a combination of the aforementioned tools, packages and techniques then you have a pretty good chance of becoming anonymous enough to slip under the radar of those who are looking for people to snoop on. Plus, you’ll be protecting yourself from a huge number of potential nasty internet-borne viruses, malware, and spyware elements.

