What is Tor?
Heard the name Tor but not sure what it is? Here’s a brief introduction to The Onion Router, what using Tor Browser for privacy entails, and what .onion sites are.
Tor, short for The Onion Router, is an anonymous peer-to-peer darknet designed to enhance privacy and resist both censorship and surveillance. You can use it to access both standard websites with a bit of extra privacy and security and special .onion sites that can only be reached when connected to the Tor network.
The term “darknet” has all sorts of ominous undertones, but its modern usage simply refers to a network of computers that uses the internet to send data but is only accessible by using specific software, networking configurations or authorisation (passwords, keys, or IP address-based restictions for example).
The general term “overlay network” is used to describe this practice of running one communications network on top of another. In practice, a darknet has a lot in common with an an enterprise VPN, where people working remotely connect to their office network and are assigned a local address with local access to that network.
People tend to use the term “darknet” in the same breath as the “dark web. As we’ve established, a darknet is a network of computers that use the internet’s infrastructure to host and send data that’s only accessible to people using the right tool to access it, such as the Tor network.
The dark web consists of websites that are only available via a darknet, such as onion sites on Tor. The deep web refers to sites that aren’t indexed by search engines, ranging from sites and services that require a login to access to pages with no links leading to them from elsewhere on the web. Many onion sites are not indexed anywhere and can only be accessed if you have a direct address for them, making them deep web sites.
The normal web outside Tor is, by comparison, referred to as the “surface web” or “clear web” – I’ll be using the latter term in this article.

Save 81% on a VPN with SurfShark
Surfshark has dropped the price of its VPN to £1.94 a month. Head over to Surfshark now to pay a one time price of £46.44 for 24 months of Surfshark and save 81%.
- Surfshark
- 81% off
- £1.94 a month
Precautions and privacy
When you’re connected to Tor, for example via Tor Browser, your ISP can see that you’re connected to a Tor relay, but your traffic is encrypted. As with VPNs, this layer of anonymity only works until you sign into a service linked to your identity, such as Google or Facebook, so it’s probably best not to do that.
Some services, such as secure email provider ProtonMail, have dedicated onion sites and can be securely connected to via Tor, but if you’re trying to be anonymous, you should keep the services you use on Tor separate from those you use on day-to-day basis.
Facebook has an onion site, too. This might be useful for contacting friends and family if you’re on the wrong side of an state-level internet communications block, but I’d personally be disinclined to trust the privacy claims of a company whose entire business model is based upon selling their users’ eyes to advertisers.
Finally, as Tor only encrypts TCP traffic, you should avoid using services such as Skype, which can leak your originating IP address via UDP. For similar data leakage reasons, you shouldn’t use it for torrenting.
Installing Tor Browser
Getting onto Tor is trivially easy these days. Go to https://www.torproject.org/download/ and download the correct version for your OS. Run it and you’ll get a connection screen. You’ll probably want to tick the box to tell it to always connect automatically, so that you’re immediately connected to the Tor network whenever you start the browser.
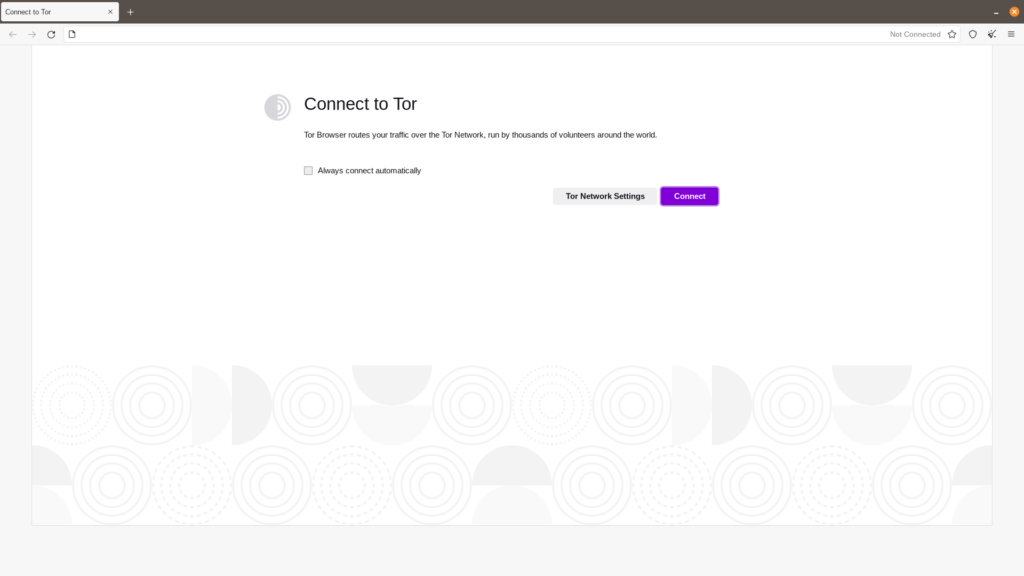
If you’re in a country or connected via a service that attempts to actively block Tor, you may need to configure the browser’s Tor Network Settings to use a bridge, but most users can ignore the advanced settings until they have specific need of them.
What’s on Tor?
By default, Tor Browser uses the Tor version of the Duck Duck Go search engine to allow you to search the clear web as normal, just it accessing via Tor for extra privacy. This is the most significant use for most people.
If you want to access onion sites, however, you’ll need to take a few more steps, though we don’t recommend any reader do this unless they have a specific, legal, need.
Many prominent onion sites are promoted on the clear web. For example, the BBC lists its onion sites, launched in 2019, on an easily-searchable clear web site. You’ll find its main English-language dark web service at https://www.bbcnewsd73hkzno2ini43t4gblxvycyac5aw4gnv7t2rccijh7745uqd.onion/. You’ll find others discussed on clear web Tor enthusiast forums, such as r/Tor.

Save 81% on a VPN with SurfShark
Surfshark has dropped the price of its VPN to £1.94 a month. Head over to Surfshark now to pay a one time price of £46.44 for 24 months of Surfshark and save 81%.
- Surfshark
- 81% off
- £1.94 a month
Many journalists and publications use SecureDrop (http://sdolvtfhatvsysc6l34d65ymdwxcujausv7k5jk4cy5ttzhjoi6fzvyd.onion/) so that sources can anonymously share documents and blow the whistle with reduced risk of exposure.
Meanwhile, on Tor itself, old-fashioned link directories exist alongside a handful of onion spiders. Just don’t expect the glossy efficiency of Google and Bing search, as onion sites tend to be resistant to traditional automated search engine robots.
Although law enforcement and other government agencies cheerfully browse, use, seize and run sites on Tor, it’s a largely unregulated and unfiltered space – you’ll only hear from said agencies if you’ve been up to anything you shouldn’t have and get caught up in one of their sweeps of illegal activity.
Expect to see more scams, malware, phishing attacks, random porn, doxxing sites, money laundering, and bootleg wares when casually browsing than you’d get on the clear web. This is vaguely interesting as both a throwback to certain parts of the early web and as a glimpse of the internet’s seedy underbelly, but if you’re not here for security reasons, the low-grade dodginess gets old fast.