How to secure your home network from hackers

A guide to the risks that come with being online and securing your home network against hackers.
Hacking still has that semi-romantic feel to it that it did back in eighties. A Wargames like fascination with being able to crack into a super secure server on your home system, complete with green text on a black background, discarded pizza boxes, and countless mugs of unfinished coffee.
However, the reality is far darker. As we’ve seen in the past it’s not just government departments, missile silos, or corrupt dictators that get on the wrong side of hackers, it’s more often normal folk like us.
There have been some pretty high profile hacking cases in recent years, the most infamous of late being the various celebrities who have had their pictures and videos stolen from their cloud accounts. These are the ones that hit the headlines, but these handful of hacking incidents are nothing compared to the millions of attempts that occur every day to the rest of us.
Related: How to become anonymous online
Hacking facts
According to the Trustwave 2013 Global Security Report (goo.gl/y3hBsE), there was a recorded 12.6 million victims of hacking and identity theft in a 12 month period through 2012 to 2013. A number which roughly equates to one person being hacked every three seconds, or so.
Related: How to remote desktop to another PC
In 2012, 98% of all hacking attacks were credit card, or payment data theft used in fraudulent online or at the till transactions. Over $21 billion (£13 billion) was estimated to be have been lost to identity theft from hackers, with a potential loss averaging $4,900 (£3,041) per household.
The checklist of items the hacker tends to go for are usernames, passwords, PINs, National Insurance numbers, phone and utility account numbers, bank and credit card details, employee numbers, driving licence and passport numbers, insurance documentation and account numbers, and any other financial background account details.
How they get this data ranges from acquiring remote access to your computer, SQL injections to a popular website, spoofing a banking or other financial website, remote code execution, exploits in website trust certificates, physical theft, and through social media.
On the subject of social media there are some interesting numbers associated with it. According to sources, 16% of people under the age of 19 were the victims of a controlled phishing scam, and 72% were victims when they followed links posted by their friends. Furthermore, 68% of all social media users share their birthday information publically. 63% shared the schools, colleges and universities they attended. An amazing 18% of users publically share their phone numbers, and 12% share the names of their pets (more on this later).
Related: Best laptop
If these numbers aren’t scary enough, there’s the fact that 19% of all Wi-Fi users worldwide are still using WEP encryption for their home network security. And, 89% of all public Wi-Fi hotspots are unsecured, unmonitored, and available all day, every day.
And finally, it’s estimated that 10% of all spam emails are malicious and contain some kind of injection code designed to infiltrate your system if they are opened. And a further 7% of all spam emails contain a link to a website that has been designed to steal information or download some element to gain access to your locally stored data.
What to do
We have put together a number of steps to help you try and prevent someone from hacking into your personal space, whether that’s in the cloud or on the computer in front of you.
Naturally you can take all these steps to the extreme and live in an electro-shielded, anti-spy cage complete with tinfoil hat and lead-lined roof. However, that’s not really an option for most people. There is though, a happy medium where you can do everything you reasonably can to protect yourself and, more importantly re-educate yourself to spot potential hacking attempts and successfully monitor the security of your home network.
Network protection
Starting with the home network there are a number of easy steps we can take to stop the hacker from gaining entry to your systems. Most of these steps you probably already do, and some are surprisingly simple.
Change router administrator passwords
This is one of the most common points of entry for someone to gain access to your home network. The router you received from your ISP may well be up to date and offer the best possible forms of encryption, but they generally all come with a set number of WiFi SSIDs and wireless keys – usually printed on the rear of the router.
It doesn’t take much of a genius to trawl the less reputable sections of the internet and obtain a list of SSIDs and wireless keys used by that particular ISP. The fact that your router is near permanently advertising itself as a BTHomeHUB, Sky, TalkTalk or whatever model doesn’t help much either.
Related: Best free antivirus
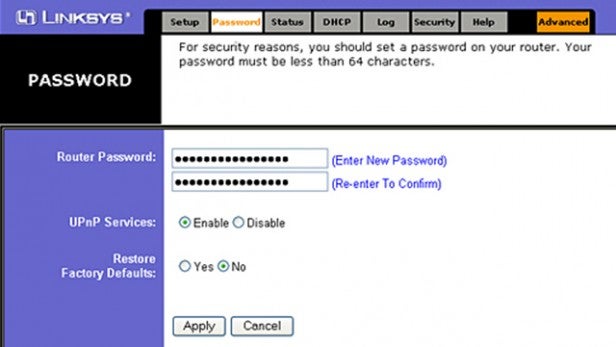
The canny hacker can therefore gain access to the router, establish a connection, and even use the list of default passwords, such as login: Admin, password:1234, in order to get into the inner workings of the router itself. Therefore, it’s best to change the default router usernames and passwords to something a little more complex and personal.
Check wireless encryption
Most routers come with a level of encryption already active, but there are some examples where the default state of encryption may be extremely weak, or worse still, completely open.
If there’s a padlock next to your wireless network, as seen from scanning for wireless networks on a computer, then you at least have some encryption active. If you then access the administration layer of your router and it tells you that the encryption method is anything other than WPA2, then you’ll need to change it pretty sharpish.
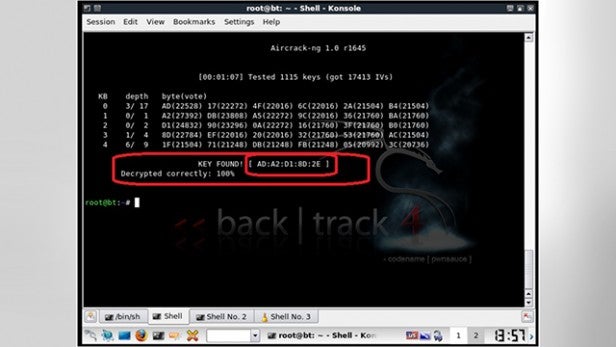
WEP is the older standard of wireless encryption and as such can be cracked in less than fifteen minutes through a number of clever tools, all of which are freely available. WPA and WPA2 aren’t perfect either, but the encryption is generally tough enough to dissuade any street level hacker.
Use MAC address filtering
Every network interface has a unique identifier known as a MAC (Media Access Code) address, regardless of whether it’s a computer, tablet, phone, or games console.
The idea behind MAC address filtering is simple enough. You obtain the MAC addresses of your devices at home and enter them into the router so that only those unique identifiers are able to connect to your network.
Obviously, if you have a significant number of network capable devices this could take some time. But in theory you should be a lot more secure against a hacker in a car outside your house with a laptop perched on their knees.
Unfortunately MAC addresses can be hacked and spoofed, so while the lesser hacker may give up the more determined one will simply bypass it. Think of MAC address filtering as putting a thorny rose bush up against the garden gate; it may stop most opportunists from entering your garden, but those who really want to get in there will find a way.
Disable SSID broadcast
There are two schools of thought when it comes to hiding your network SSID. The first recommends hiding your router’s SSID from the public view, with the idea that invisibility to those around you makes you somehow immune to their attempts.

For the most part it’s good advice, but those against hiding network SSID say that anyone with half a hacking brain is already using some sort of SSID sniffer, and should they come across a hidden network it’ll pique their interest more than your neighbour who isn’t hiding it.
It’s worth considering both sides of the argument. Are you successfully hidden by being invisible, or is the best hiding place in plain sight?
Use static IP addresses
By default your router will automatically assign an IP address to any device that connects to it, so the pair, and the rest of the network, can communicate successfully.
DHCP (Dynamic Host Configuration Protocol) is the name for this feature, and it makes perfect sense. After all, who wants to have to add new IP addresses to new devices every time they connect to your network?
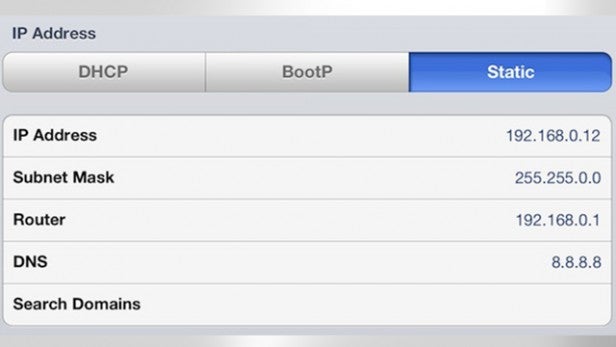
On the other hand, anyone who gains access to your router will now have a valid IP address which allows it to communicate with your network. So to some degree it’s worth considering opting out of DHCP controlled IP addresses and instead configuring your devices and computers to use something like 10.10.0.0 as their range of IP addresses.
Like most good anti-hacking attempts though, this will only slow the intruder down.
Router position
This simple network protection act is one of the best, if done correctly.
Believe it or not, by moving your router to the centre of your house, or more to the rear (depending on where your closest neighbours or the road is), you are limiting the range of your wireless broadcast signal.
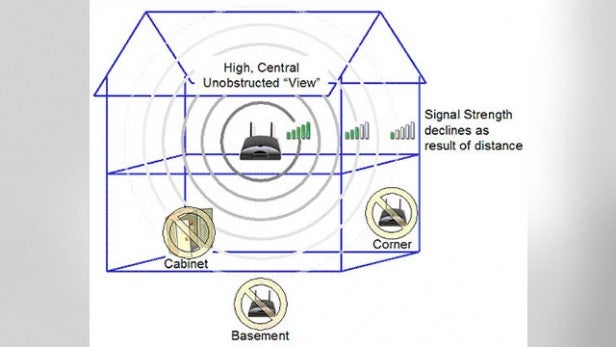
Most routers are located in the front room where the master phone socket usually is. This means the router can reach most corners of the house, and to some degree beyond the house. If someone was moving down the road, for example, sampling wireless networks then they would come across yours as they passed your house.
If the router is situated in a more central location, away from the front window, then the signal may be too weak to get a successful reading without having to stand on your porch.
Switch off the router when you’re not using it
Most people will already do this anyway. Since no one is using the router, what’s the point of wasting electricity?

However, a lot of people simply have their router powered on all the time, regardless of whether they are in the house or not. Granted there are those who will be running a server, or downloading something while at work or asleep, but the vast majority just keep it on.
If you’re not using the internet or any other home network resource, it’s a good idea to power off the router. And if you’re away for an extended period, then do the same.
Beyond the home hardware
Home network security is one thing, and frankly it’s not all that often you’ll get a team of hackers travelling down your street with the intent of gaining access to you and your neighbour’s home networks.
Where most of us fall foul in terms of hacking is when we’re online and surfing happily without a care in the world.
Passwords
Passwords are the single weakest point of entry for the online hacker. Face it, how many of us use the same password for pretty much every website we visit? Most of us even use the same password for access to a forum that we use for our online banking, which is quite shocking really.
Using the same password on every site you visit is like giving someone the skeleton key to your digital life. We know it’s awkward having different passwords for different places, but when you stop and think logically about it, doing so leaves you incredibly vulnerable to those who have ill intentions with regards to your identity and bank balance.

Also, where passwords are concerned, using ‘12345’, ‘password’, or ‘qwerty’ isn’t going to stop someone from gaining access. And passwords such as ‘P4ssw0rd’ aren’t much better either. Furthermore, as we mentioned earlier, using the names of your pets may seem like a good idea, maybe even mixing their names with the date of your birth as well sounds like a solid plan, but if you then go and plaster Mr Tiddles, Fluffly, or Thumper’s names all over the public-facing side of social media along with ‘it’s my birthday today, yippee’ then you’ve just seriously negated any chance of your passwords from remaining secret.
Security questions and two-phase, or two-step, verification password techniques are now being employed by a number of credible sites. What this means is that you basically enter more than one password to log into your account. Most online banking is done this way now, and sometimes includes a visual verification such as a pre-selected thumbnail image from a range that the user can click on to verify who they are.
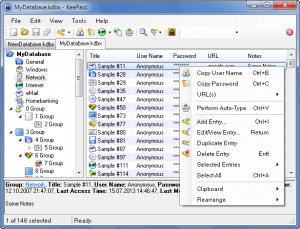
If you have trouble coming up with passwords yourself, then there are a number of password managers available that can help you create highly secure combinations of letters, numbers, and special symbols unique for every website you visit. What’s more they’ll even store them for you in the program itself in case you forget what they are:
KeepPass – A free open-source password manager which can help you keep track of your passwords across numerous sites, while still being safely locked away in a secure database.
LastPass for Safari for Mac – A free plugin for Safari and Mac users, LastPass allows you to create a single username and password while securely entering the correct details.
Kaspersky Password Manager – A fully automated and powerful password manager that can store your username and password details, then enter them into the site for you while remaining encrypted throughout.
Either way, human beings are the weakest link in the secure password chain so any help you can get isn’t a bad thing.
Don’t share so much
Lance Ulanoff, the chief editor at Mashable, recently said. “I hate to say it, but the reality is people need to share a little bit less.”
While there’s nothing wrong with letting our friends and family know what we’re up to via social media, we have to consider the fact that they may not be the only ones watching. Facebook and Twitter often come under fire regarding public newsfeeds where you have to run through several clicks before you can limit the views for your own timeline.
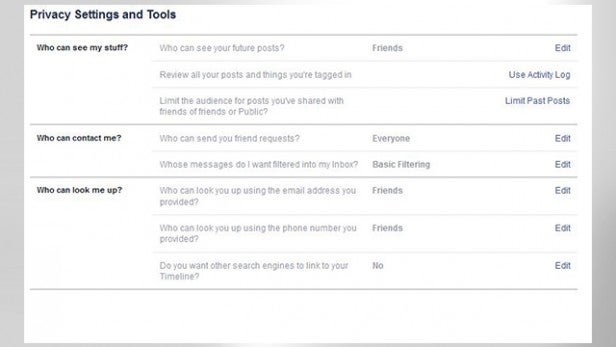
It’s worth taking the time to double-check, and check back often, the security settings on all your social media sites. Are the things you’re posting on your timeline or feeds viewable by friends only, or friends of friends? Has it mysteriously been reverted back to public viewing? Are you sure you want to display that picture of your cool desktop wallpaper complete with conky-like network information in the corner?
As we said before publically announcing private details, like when you’re on holiday and for how long, the names and birthdays of you, your partner, your children, pets and so on, isn’t a particularly wise thing to do. But we’re all guilty of it.
Security in the cloud
The newsworthy hacking events of Jennifer Lawrence and her celebrity colleagues has nailed home to the average user the fact that cloud storage isn’t quite as secure as they initially thought.
Every device, either Android, Microsoft, or Apple, is capable of backing up your photos to its own particular cloud storage solution – sometimes it’s even a default setting. Most of the time the cloud solutions used are so secure that anyone trying to hack into them will have a pretty rough time of it, and no doubt bring down the wrathful vengeance of Google or Apple upon themselves. How the celebrity photos and videos were obtained is something you’ll have to find out for yourselves, but if storing stuff on the cloud is alarming you there are a couple of choices.
The first is to encrypt everything locally on your computer before uploading it to the cloud. This will take time, we’ll grant you, but it means only you’ll be able to decrypt them. Secondly, you could always compress everything first, using Winzip/Winrar etc., then password the compressed file. Breaking a password compressed file takes far longer than it’s actually worth, providing you’re not a celebrity, so most hackers won’t bother.
Finally, there are cloud storage solutions that encrypt the data on the device before uploading it to the also fully encrypted servers. The likes of SpiderOak and Tresorit already do this.
Use a VPN
When you connect to the internet you do so through the IP address given to you by your ISP (your external IP address that is). Essentially this address is a batch that the ISP own, and everywhere you go on the internet that address is highlighted and can be traced right back to your ISP and in particular, you.

If you opt to take out an account with a Virtual Private Network service, like CyberGhost or HMA! or TOR, then the IP address you use will come from the VPN’s servers, which are located around the world. So the website you visit will highlight your IP address as coming from Iceland, where in actual fact you’re located in Barrow-in-Furness, or wherever.
It’s not perfect, but it’s certainly a level of protection that’s worth looking into.
Email encryption
Of the millions of emails sent and received by the hour only a handful are ever encrypted. Most internet users have one of the free webmail accounts, such as Google or Yahoo, and although there is some level of encryption involved it’s generally not enough to stop a determined hacker.
If you want total encryption of your email, or webmail, you’re going to have to use one of the many encryption programs available that work as a third party tool in conjunction with an email client.
There are plenty around, and they work with Thunderbird, Outlook, Pegasus, and countless other clients. Also, there are web-based encryption tools available, like FireGPG, which will install inside of Firefox or other browsers and encrypt web pages and more importantly any emails sent via a webmail service.
Conclusion
Despite all of the above, the very fact that you’re online makes you a potential target. It’s no use sitting back and saying “they’ll have no interest in me”, when it’s you the hacker wants to target. After all, you’re easy to get to, easy to hack, and won’t launch a huge international campaign should you get hacked.
In other words, it pays to be aware of the risks and how to ensure against them.

